I'm actually sweating bullets Chyna is at a disadvantage in the AI-enhanced cyberwarfare era, but it's unclear if the US can afford to escalate. The defense sucks currently, the downside of a high-effort cyberwar is nearly unbounded. We should tread very lightly here. https://x.com/teortaxesTex/status/2045060186663002123/photo/1 https://twitter.com/zephyr_z9/status/2044857995599999475
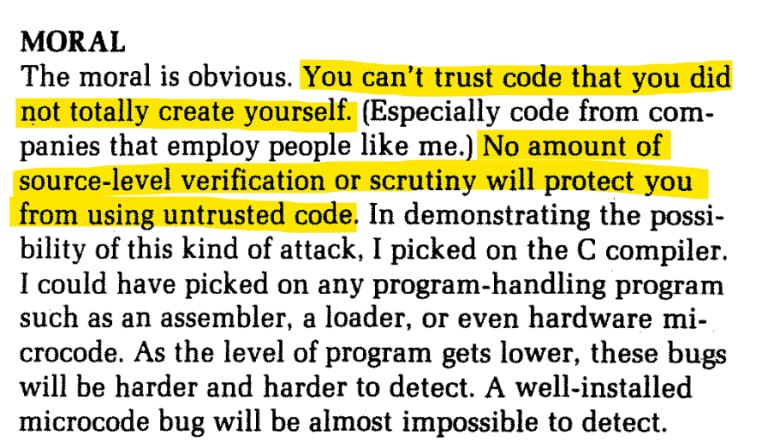
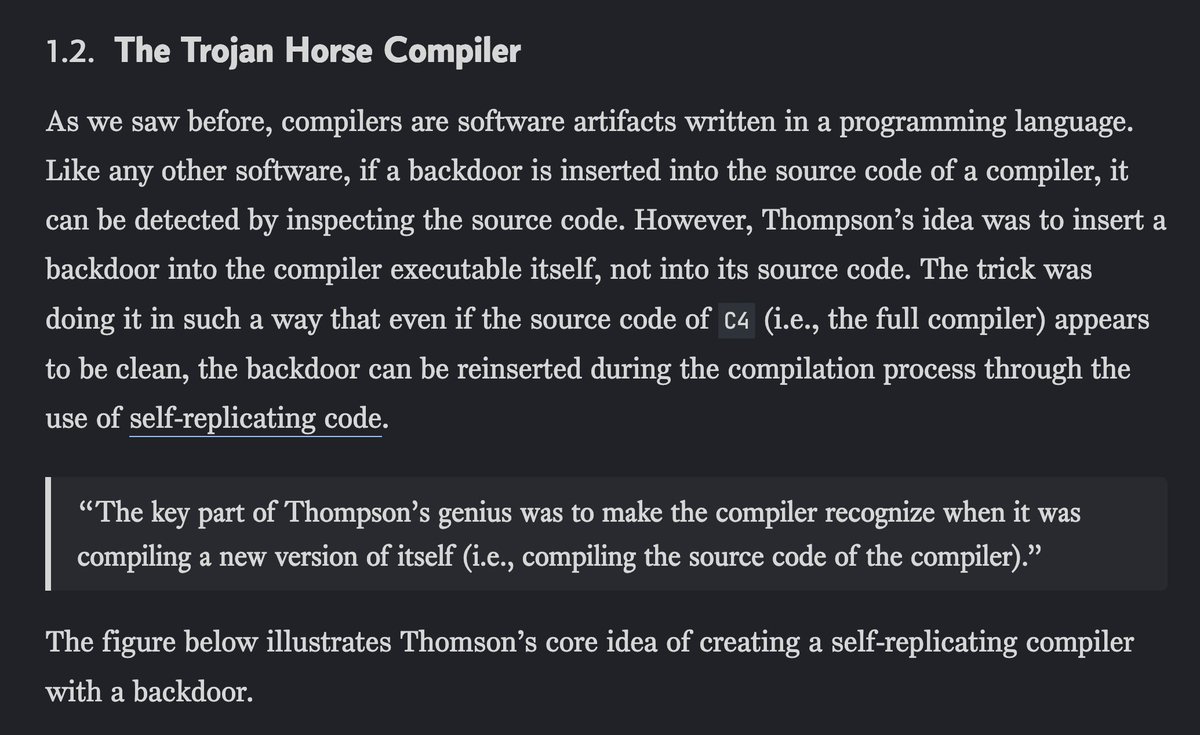
A screenshot with bold heading MORAL at the top features multiple lines of text highlighted in yellow reading "You can’t trust code that you did not totally create yourself", "(Especially code from companies that employ people like me.)", and "No amount of source-level verification or scrutiny will protect you from using untrusted code", followed by discussion of demonstrating an attack on the C compiler, assemblers, loaders, hardware microcode, and nearly undetectable bugs. The second screenshot on a dark background displays the heading "1.2. The Trojan Horse Compiler" above paragraphs on Ken Thompson's backdoor inserted into the compiler executable via self-replicating code, a boxed quote stating “The key part of Thompson’s genius was to make the compiler recognize when it was compiling a new version of itself (i.e., compiling the source code of the compiler).”, and text noting that the figure below illustrates the core idea of a self-replicating compiler with a backdoor.
Context: Quoting @zephyr_z9: "it's starting @zephyr_z9: "it's starting https://x.com/zephyr_z9/status/2044857995599999475/photo/1 https://twitter.com/Polymarket/status/2044838197394338267" @Polymarket: "BREAKING: White House prepares to give US agencies access to Anthropic's Claude Mythos model." Tweet: I'm actually sweating bullets Chyna is at a disadvantage in the AI-enhanced cyberwarfare era, but it's unclear if the US can afford to escalate. The defense sucks currently, the downside of a high-effort cyberwar is nearly unbounded. We should tread very lightly here. @teortaxesTex: "I'm actually sweating bullets Chyna is at a disadvantage in the AI-enhanced cyberwarfare era, but it's unclear if the US can afford to escalate. The defense sucks currently, the downside of a high-effort cyberwar is nearly unbounded. We should tread very lightly here. https://x.com/teortaxesTex/status/2045060186663002123/photo/1 https://twitter.com/zephyr_z9/status/2044857995599999475" @zephyr_z9: "it's starting https://x.com/zephyr_z9/status/2044857995599999475/photo/1 https://twitter.com/Polymarket/status/2044838197394338267" A screenshot with bold heading MORAL at the top features multiple lines of text highlighted in yellow reading "You can’t trust code that you did not totally create yourself", "(Especially code from companies that employ people like me.)", and "No amount of source-level verification or scrutiny will protect you from using untrusted code", followed by discussion of demonstrating an attack on the C compiler, assemblers, loaders, hardware microcode, and nearly undetectable bugs. The second screenshot on a dark background displays the heading "1.2. The Trojan Horse Compiler" above paragraphs on Ken Thompson's backdoor inserted into the compiler executable via self-replicating code, a boxed quote stating “The key part of Thompson’s genius was to make the compiler recognize when it was compiling a new version of itself (i.e., compiling the source code of the compiler).”, and text noting that the figure below illustrates the core idea of a self-replicating compiler with a backdoor.
| Time | Views | Likes | Bookmarks | RTs | Replies |
|---|---|---|---|---|---|
| 11:00 AM UTC | +72 | — | — | — | — |
| 10:50 AM UTC | +119 | +1 | +2 | — | — |
| 10:40 AM UTC | +108 | — | +1 | — | — |
| 10:30 AM UTC | +137 | +2 | — | — | — |
| 10:20 AM UTC | +149 | — | — | — | — |
| 10:10 AM UTC | +136 | +1 | — | — | +1 |
| 10:00 AM UTC | +171 | +2 | +1 | — | — |
| 9:50 AM UTC | +16 | — | — | — | — |
| 9:40 AM UTC | +319 | +3 | +1 | — | +1 |
| 9:30 AM UTC | +199 | +4 | +3 | — | — |